The legacy of fy_iceworld, Counter-Strike's divisive and hugely popular custom map | Rock Paper Shotgun

Cambridge International AS/A L Level Computer Science sample by Cambridge University Press Education - issuu
![Steam Community :: Guide :: Counter-Strike: Source Dedicated Server (SteamCMD) [English/Englisch] [Windows] Steam Community :: Guide :: Counter-Strike: Source Dedicated Server (SteamCMD) [English/Englisch] [Windows]](https://steamuserimages-a.akamaihd.net/ugc/1617175662585643783/B768999991694E0C5F0FF003F909CB1E38609134/)
Steam Community :: Guide :: Counter-Strike: Source Dedicated Server (SteamCMD) [English/Englisch] [Windows]
How to make a backup for ClearSCADA database while the hosting server is running | FAQs | Schneider Electric Brazil
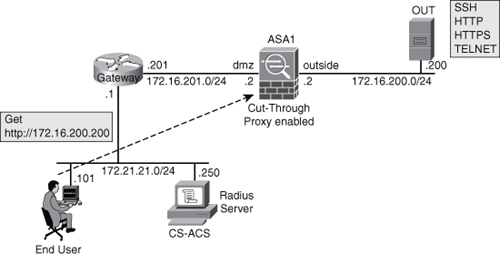
Identity on Cisco Firewalls : ASA User-Level Control with Cut-Through Proxy (part 1) - Programing4Us - Enterprise
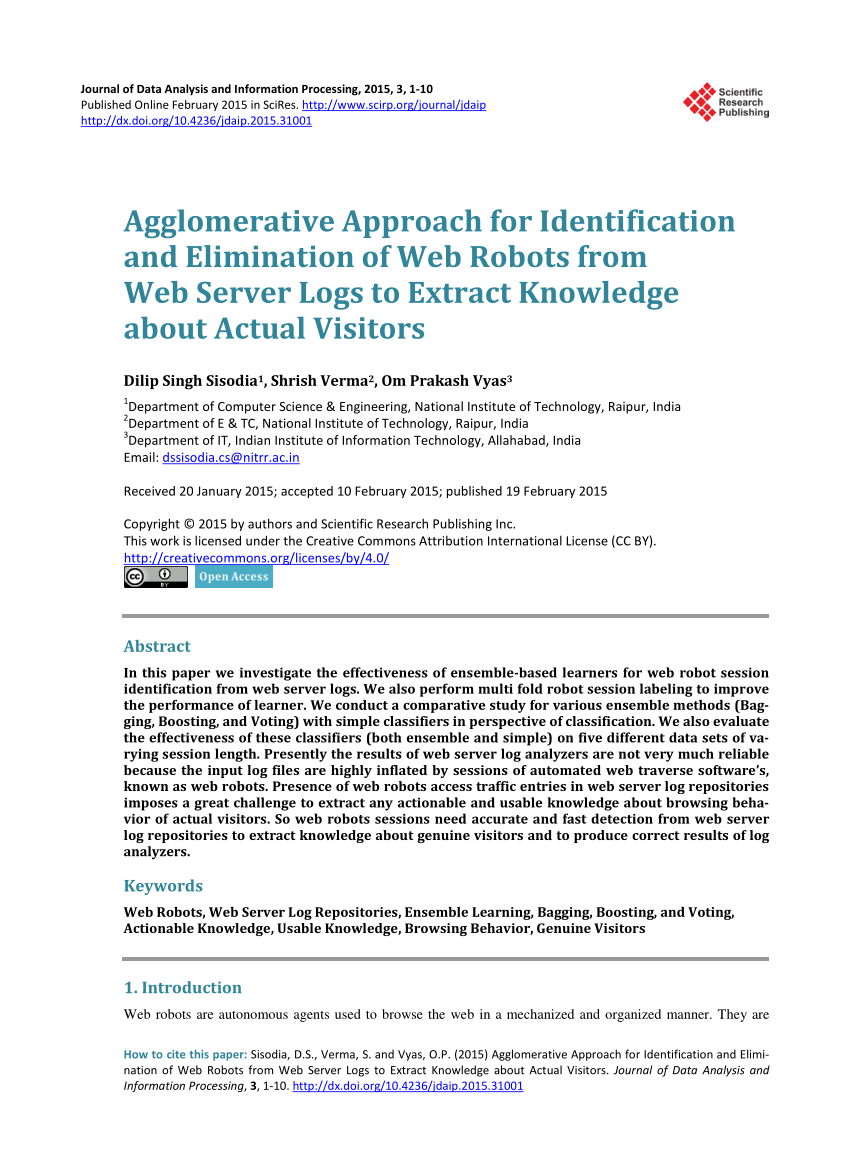
PDF) Agglomerative Approach for Identification and Elimination of Web Robots from Web Server Logs to Extract Knowledge about Actual Visitors
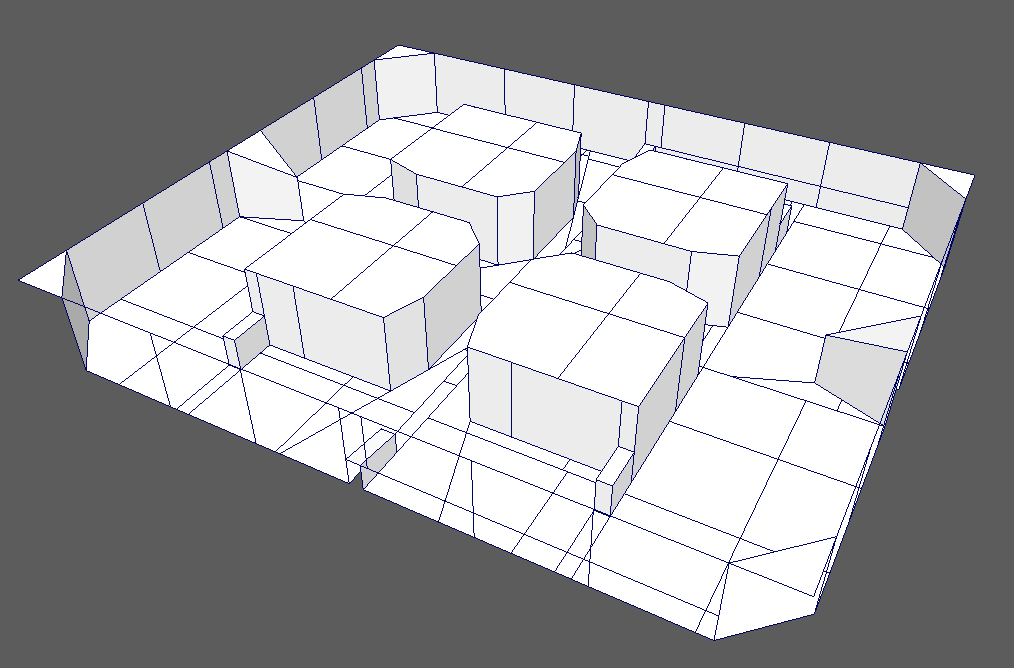
The legacy of fy_iceworld, Counter-Strike's divisive and hugely popular custom map | Rock Paper Shotgun

PDF) Development of an identity management system for a web proxy server in a tertiary institution using anonymity technology:

Table 1 from A novel dual authentication protocol (DAP) for multi-owners in cloud computing | Semantic Scholar